Bypass NAC and avoid detection
The Basilisk is the ultimate tool for penetration testing on Ethernet networks. Built around a dedicated hardware packet engine, the Basilisk seamlessly merges the Ethernet traffic of one device (the "ghost") into another.
On one end of the Basilisk, two Ethernet ports are available - one for the ghost and one for the legitimate host. On the other end, a third Ethernet port connects to the upstream network (switch / router).

From the legitimate device's point of view, this is fully transparent - the packets are let through unmodified.
For the ghost device however, packets will not be forwarded until the MAC address of the legitimate device is discovered by the Basilisk. Once the legitimate MAC is known, all packets from the ghost will be altered in real-time directly as they are received over the wire before being forwarded to the upstream network. The ghost's MAC address is replaced inside the packet headers to hide them within legitimate traffic. On the way back, packets coming in from the network are re-routed by the Basilisk to the ghost, again with their headers updated to make all of this fully transparent.
The Basilisk also replaces the ghost MAC address within ARP and DHCP packets to avoid detection from other mechanisms.

Network intrusion on a whole new level
This ghosting mechanism offers multiple significant advantages.
Hiding your traffic within a legitimate device's communications makes it much harder for any SOC to detect your activity. An added benefit is to not require an additional network port to connect your malicious device - simply ghost it behind some printer, desktop, or any other connected gadget instead of wasting time looking for a free port or suspiciously unplugging something.
Maybe even more importantly in many cases, this makes bypassing any NAC or MAC whitelisting a breeze. Most 802.1x implementations are instantly defeated with zero effort - in fact we have never yet seen a real-life case where the NAC was not immediately defeated by this (but we are sure they must exist :) ).
Fully automatic
Whenever you need network access, just plug through the Basilisk and instantly get connected without having to mess with any configuration. The Basilisk will discover MAC addresses and ghost your traffic automatically.
This also ensures no packet from your host will ever be let through without being ghosted. Traffic is simply dropped until the legitimate host's MAC address is discovered. No more risk of accidentally triggering port security on the upstream switch and facing port shutdowns in the field.
As long as your host is plugged into the ghost port of the Basilisk, your packets are safe.
Real-time hardware solution
The Basilisk can operate at full 10/100 Ethernet throughput thanks to its dedicated hardware packet engine. No latency is induced as a result of the operation, allowing you to intrude in silence at maximum speed.

Buffering on all ports
Every port on the Basilisk features 32KB of circular packet buffer to reduce the risk of packet loss due to congestion.
Since the Basilisk combines the packets of two Ethernet devices into a single output port, congestion may occur during peak activity. The buffers ensure maximum throughput by minimizing this.
What's included?
- Basilisk (main board)
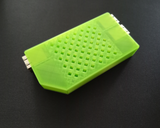
- Plastic case (green)
- 12V 1A power supply
- 3x Cat6 cable (1m)

Please note: the power supply provided with the Basilisk outputs 12V, which is not suitable for the Skunk. Be careful not to use the wrong power supply with your device.
The Basilisk is shipped with a basic 3D-printed press-fit enclosure. This means you can easily swap the case and print your own, or even integrate the Basilisk board directly into something else.
STL files for the included case are provided below, ready to be 3D-printed.
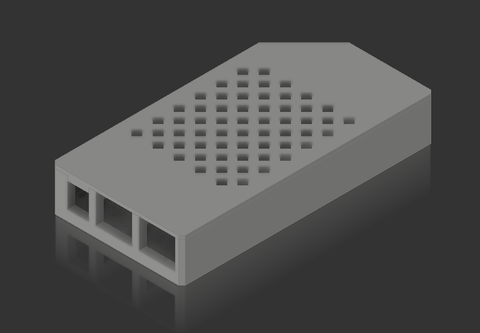
Two files are provided - one for the bottom of the enclosure and one for the top.
IMPORTANT NOTE: THIS IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED.
IF YOU ARE PURCHASING THIS, IT IS ASSUMED YOU KNOW HOW TO USE IT AND WHAT YOU ARE DOING.
THAT BEING SAID, YOU ARE REQUIRED TO OBEY THE LAW AND ARE PROHIBITED FROM USING RINGTAIL PRODUCTS FOR ANYTHING OTHER THAN LEGITIMATE PURPOSES.
RINGTAIL WILL NOT BE HELD RESPONSIBLE FOR ANY DAMAGE CAUSED AS A RESULT OF USING OUR PRODUCTS.